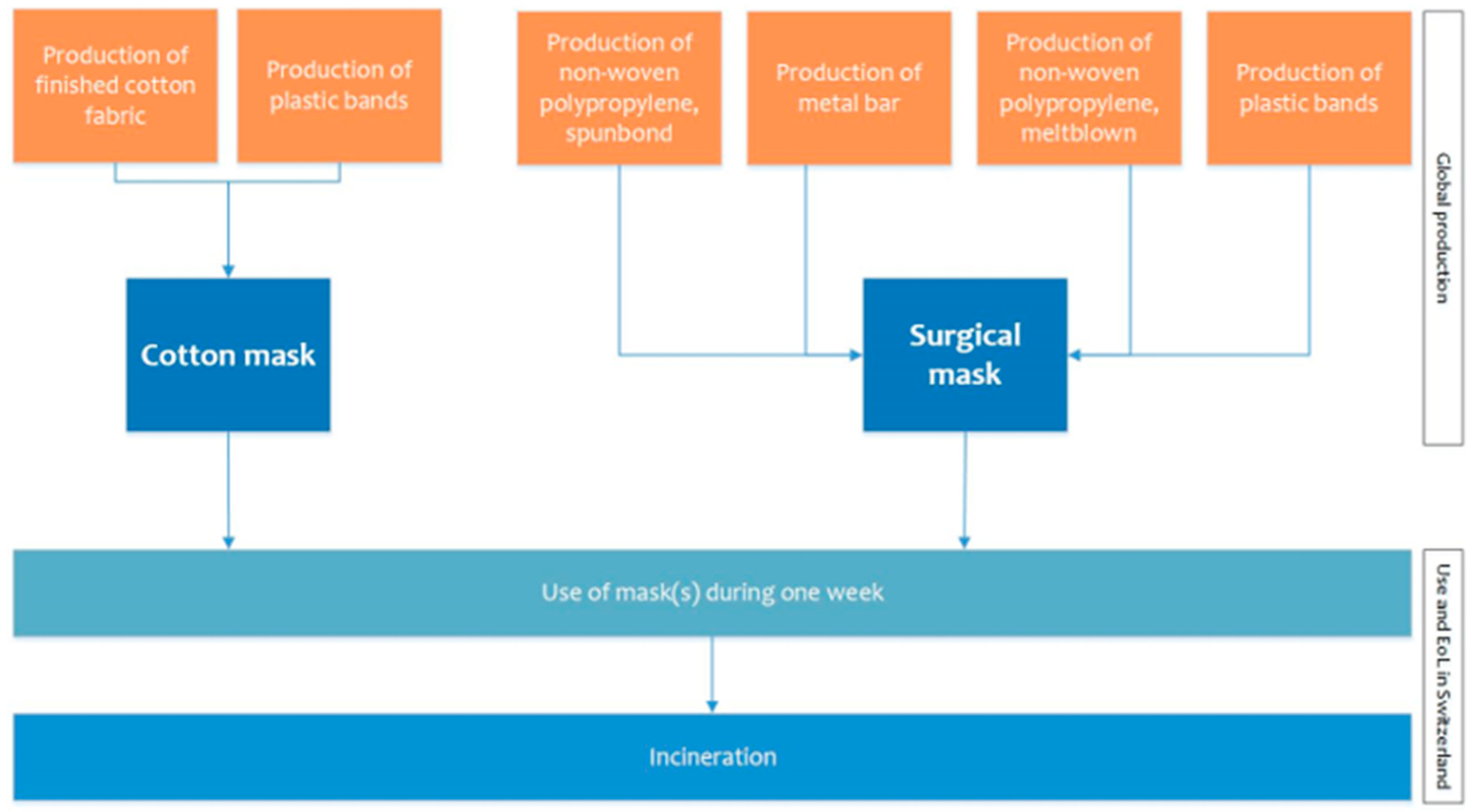
Sustainability | Free Full-Text | Cotton and Surgical Masks—What Ecological Factors Are Relevant for Their Sustainability?

VA proposes updates to disability rating schedules for respiratory, auditory and mental disorders body systems - VA News
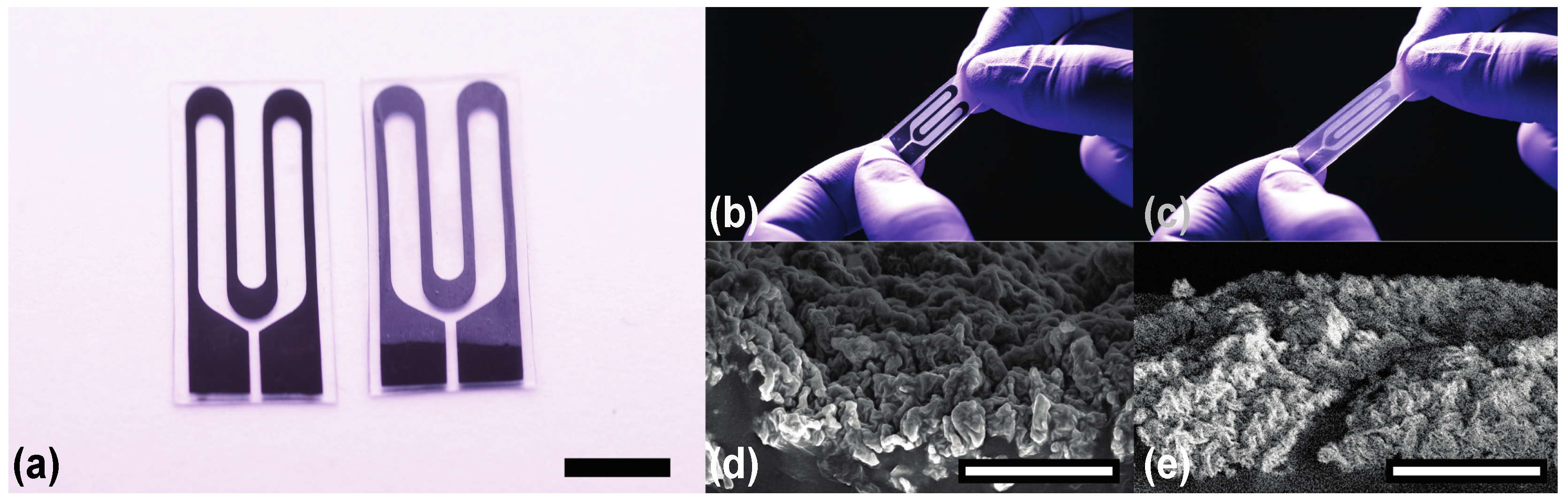
Materials | Free Full-Text | The Effect of Encapsulation on Crack-Based Wrinkled Thin Film Soft Strain Sensors
Proxies and Configurations Used for Credential Stuffing Attacks on Online Customer Accounts - HS Today

Deep learning approaches to semantic segmentation of fatigue cracking within cyclically loaded nickel superalloy - ScienceDirect

FDA revokes emergency nods for KN95 respirators and disinfecting hardware as mask supplies rebound | Fierce Biotech

Measuring the Particle Packing of l-Glutamic Acid Crystals through X-ray Computed Tomography for Understanding Powder Flow and Consolidation Behavior | Crystal Growth & Design

We're a people destroyed': why Uighur Muslims across China are living in fear | Xinjiang | The Guardian

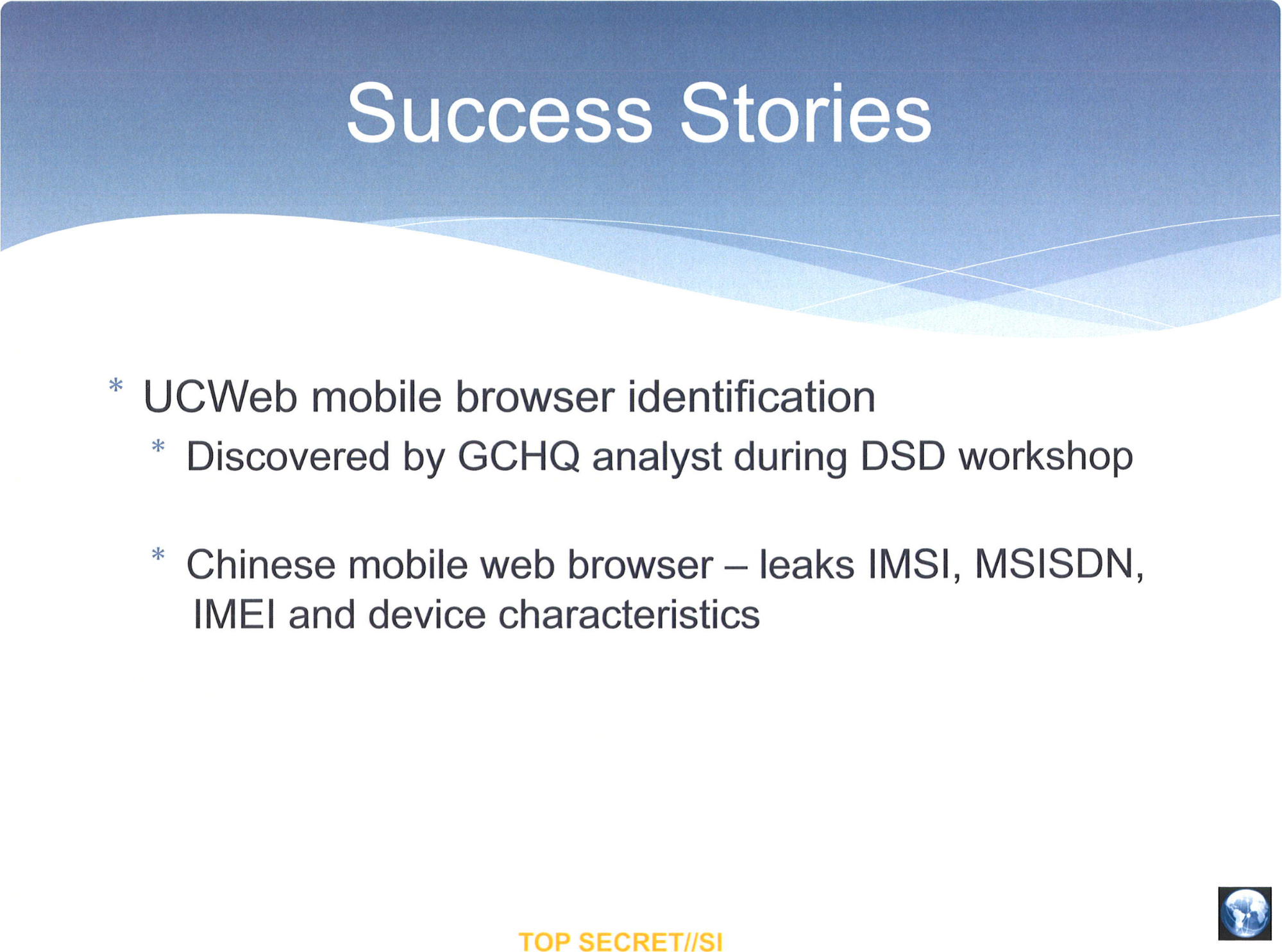



![Hacking clients with WPAD (web proxy auto-discovery) protocol [updated 2021] | Infosec Resources Hacking clients with WPAD (web proxy auto-discovery) protocol [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2014/07/013021-5.png)